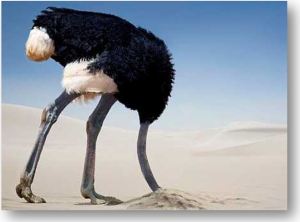
Why do ostriches bury their heads in the sand?Will encryption protect our data?
- Search for the Truth
There are so many myths to muse about! They sound great. Myths are easy to remember. They play well with others – the myth that is.
Ostriches bury their “eggs” in the sand. Just for a moment – it appears to bury its head – when turning the eggs.
- Don't bury your head in a myth
Encryption protects communication. Just for a moment – it appears to protect static data – if no one ever steals it.
Let’s take a closer look.
Have you seen the “Imitation Game”? Even though the Enigma machine was adhering to its truest purpose, protecting communication, Turing broke the encryption - daily.
Think of encryption as a safe. It is a good safe. The locking mechanism is very good – prime numbers. So what’s the problem?
Just like in the “real world”, if someone steals the “entire safe”, they get the contents as well. Once that safe is in their back yard, it is only a matter to time!
What evidence is there that encryption can be broken?
When eBay’s breach occurred back in 2014, their user base, complete with encrypted passwords was stolen. That’s right, encrypted passwords. And what did they say? “Change your passwords”. Why would they warn users to change their passwords when they were encrypted? Isn’t the answer obvious? Those in the industry know the answer!
Encryption can be broken.
Encryption can be broken.
Adele’s Photo Hack (like other celebrities) involved combinations of iCloud and email services. Bottom line, encryption can be broken.
The Cloud needs a security service that supersedes encryption.
The Cloud needs a security service that supersedes encryption.
In simple terms, prime numbers are the keys that lock and unlock encryption. 128-bit encryption versus 256-bit encryption tells us how large these keys are. They are very large. The larger they are, the more difficult it is to find the key. So where’s the problem?
Computers are more powerful every day. Prime number generators exist. Modern computers equipped with prime number generators can do in seconds what it would have taken Turing’s computer, years to compute during the second world war.
What’s the alternative? We need to do something to protect our data in the Cloud.
- CORA Cyber Security Inc.
The answer is CORA (Context Ordered Replacement Algorithm). Read more about this “unbreakable data security” at http://CORAcsi.com and download your free CORA Explorer at http://CloudCORA.com .


CORA Explorer is for Windows. Do you have a mobile app?
ReplyDeleteNot at this time. The Windows based CORA Explorer satisfies two goals for CORA:
ReplyDelete1) Proof of concept.
2) A pathway by which individuals may enter the "CORA Challenge" which will be released to the public shortly.
CORAcsi plans to release later this year:
A) goCORA - a mobile app that allows Registered Users to gain control over their online footprint. Initially this will empower the sharing of graphics and text such that the author may instantly "shut down" their "shared content" using CORA
B) CloudCORA as an online data storage, backup and synchronization solution - based upon CORA - the unbreakable solution.